G Network Configuration for Secure Identity Management
In today's digital landscape, securing identity management is a top priority for organizations looking to protect their sensitive data and prevent cyber threats. One critical aspect of this process is configuring a secure network architecture that supports identity management. This article will delve into the world of G Network Configuration for Secure Identity Management, exploring its importance, best practices, and solutions for implementation.
What is G Network Configuration?
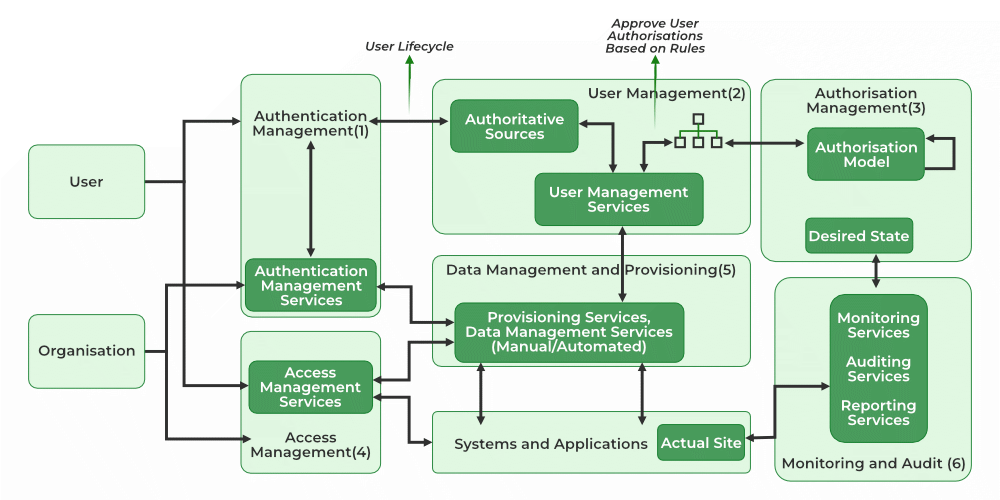
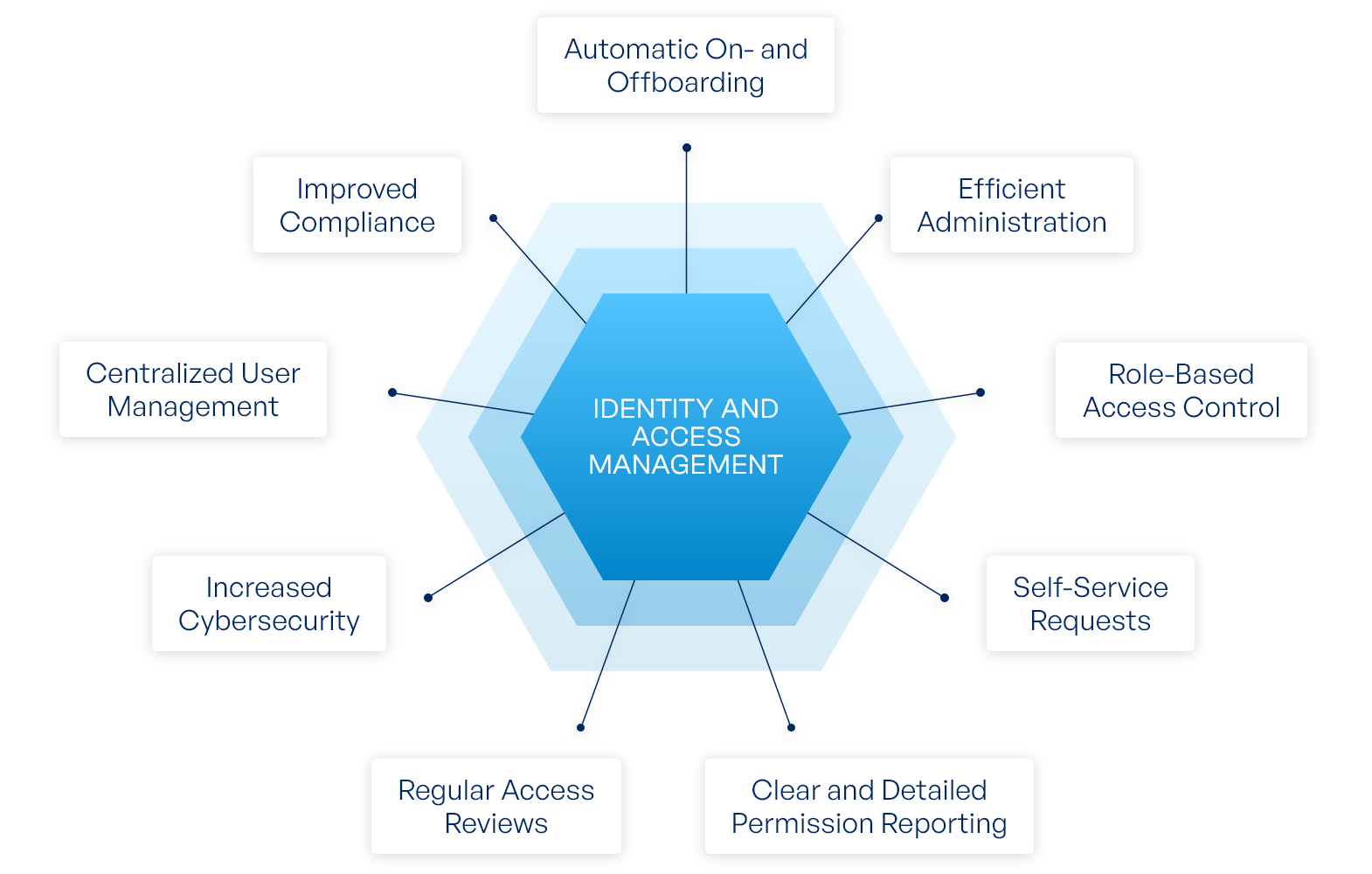
G Network Configuration refers to the process of setting up a secure network infrastructure that enables robust identity management. This involves configuring firewalls, access controls, and authentication mechanisms to ensure that only authorized users can access sensitive data and systems. By implementing a secure G Network Configuration, organizations can protect themselves against cyber threats, such as unauthorized access, data breaches, and identity theft.
Benefits of G Network Configuration for Secure Identity Management
- Improved Security**: A secure G Network Configuration provides an additional layer of protection against cyber threats, reducing the risk of unauthorized access and data breaches.
- Enhanced Compliance**: By implementing a secure G Network Configuration, organizations can ensure compliance with relevant regulations and industry standards, such as HIPAA and PCI-DSS.
- Increased Efficiency**: A secure G Network Configuration streamlines identity management processes, reducing administrative burdens and improving user productivity.
- Better Data Protection**: Secure G Network Configuration ensures that sensitive data is protected from unauthorized access, reducing the risk of data breaches and identity theft.
Best Practices for G Network Configuration
To ensure effective G Network Configuration for Secure Identity Management, follow these best practices:
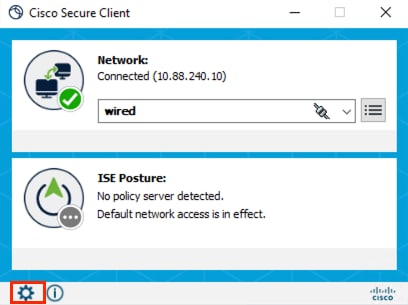
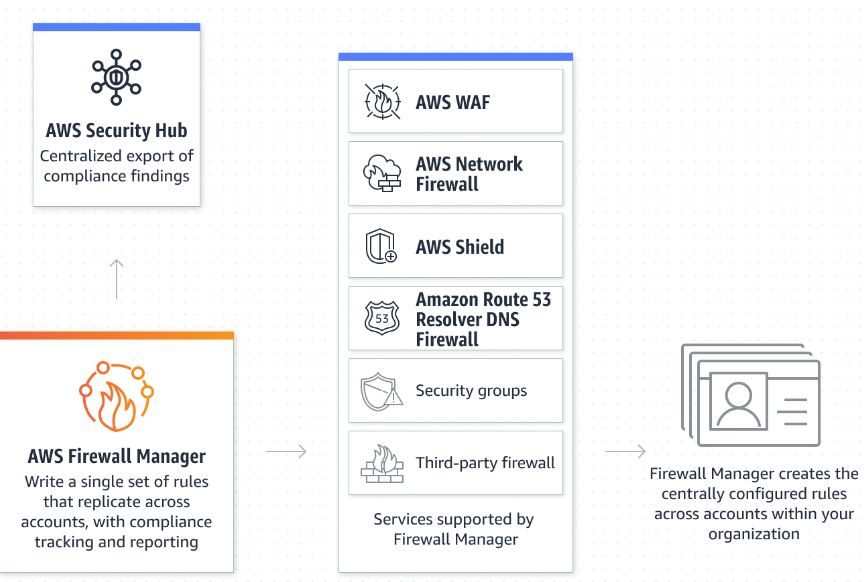
- Implement Firewalls and Access Controls**: Configure firewalls and access controls to restrict access to sensitive data and systems.
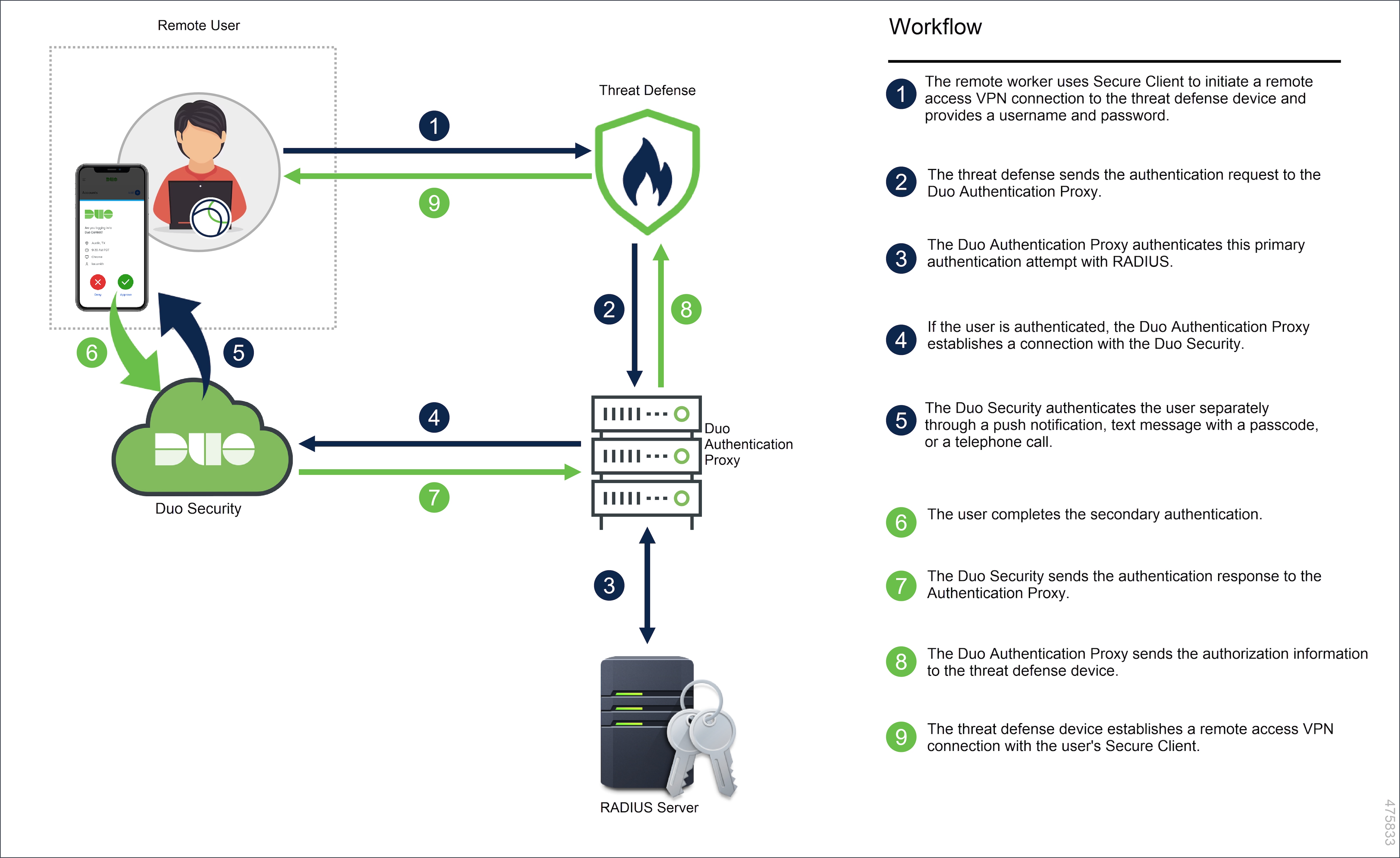
- Use Multi-Factor Authentication**: Implement multi-factor authentication to add an extra layer of security to the login process.
- Encrypt Sensitive Data**: Encrypt sensitive data to protect it from unauthorized access.
- Regularly Update and Patch**: Regularly update and patch network devices and systems to ensure that vulnerabilities are addressed.
- Monitor Network Activity**: Monitor network activity to detect and respond to potential security threats.
Solutions for G Network Configuration
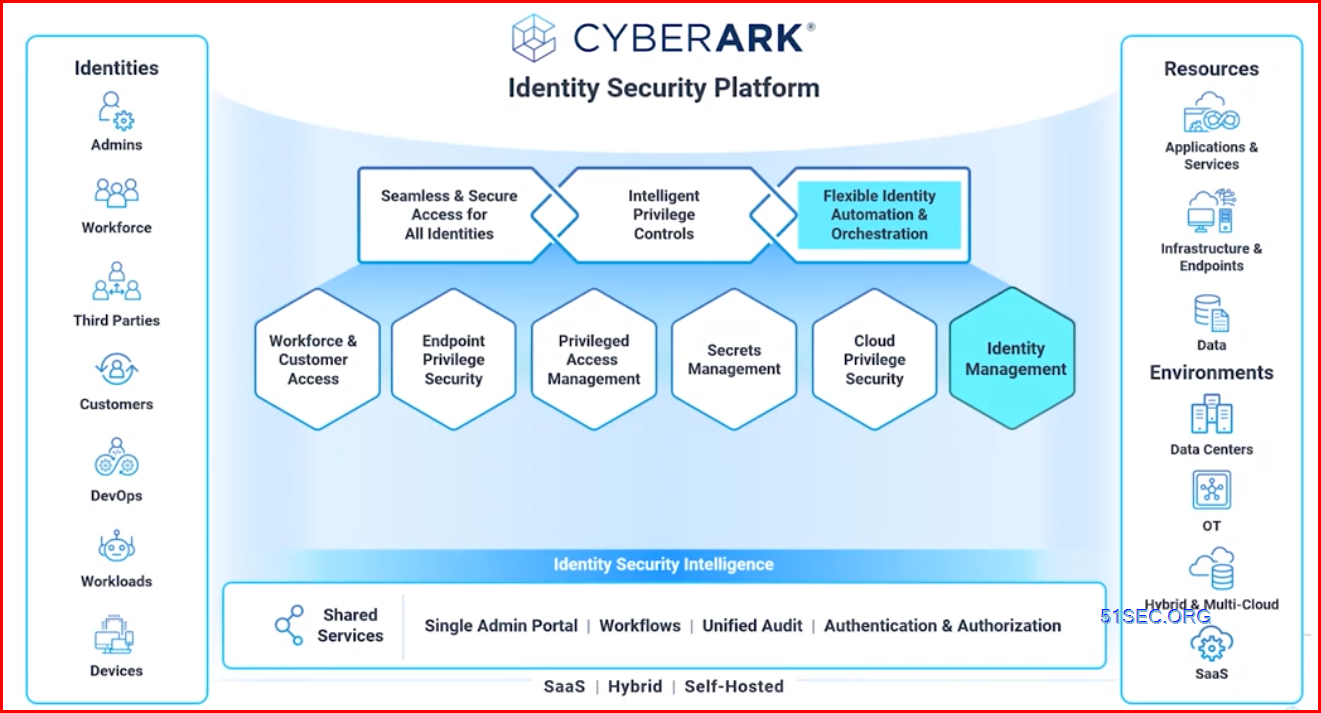
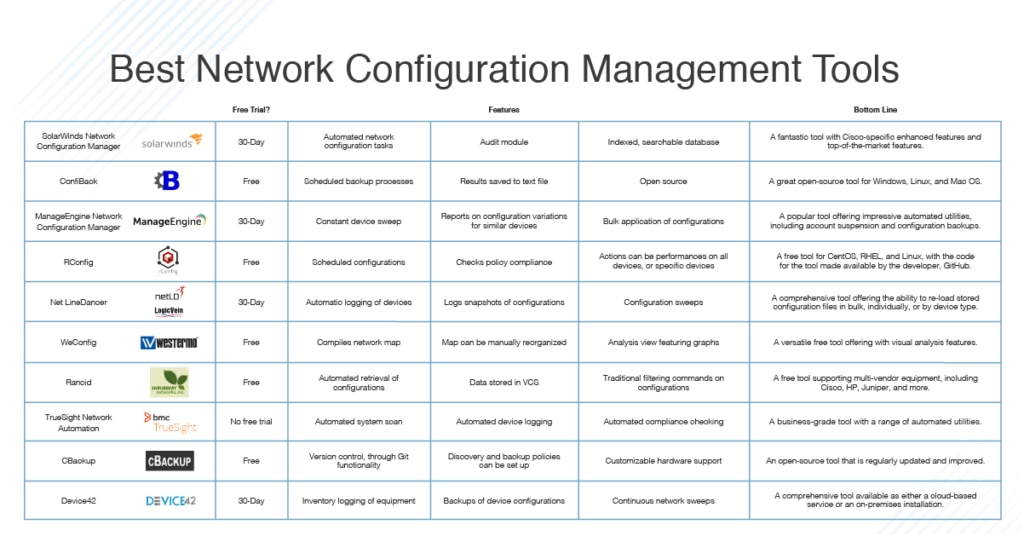
Several solutions are available to support G Network Configuration for Secure Identity Management, including:
- AWS Identity and Access Management (IAM)**: AWS IAM provides a web service for securely controlling access to AWS services.
- Google Cloud Identity and Access Management (IAM)**: Google Cloud IAM provides a unified system for managing access to Google Cloud resources.
- Infoblox DDI Platform**: Infoblox's DDI platform unites networking, security, and cloud to seamlessly integrate, automate, and secure critical network services.
- CIS Controls**: The Center for Internet Security (CIS) provides a set of best practices and controls for securing enterprise assets and software.
Conclusion
In conclusion, G Network Configuration for Secure Identity Management is a critical aspect of protecting sensitive data and preventing cyber threats. By implementing a secure G Network Configuration, organizations can improve security, enhance compliance, increase efficiency, and better protect sensitive data. By following best practices and leveraging available solutions, organizations can ensure effective G Network Configuration for Secure Identity Management.