G Wireless Network Configuration for Security Systems: Essentials for a Safe and Secure Network
As security systems become increasingly dependent on wireless networks, securing these connections is more crucial than ever. A G wireless network configuration for security systems must take into account the specific needs and vulnerabilities of these networks.
Configuring Host-Based Security Tools
One of the essential steps in securing a G wireless network configuration for security systems is configuring host-based security tools, such as host-based firewalls and host-based intrusion detection and prevention systems (HIDS/HIPS). These tools can help prevent multiple network interfaces from being used at one time, thus reducing the risk of unauthorized access.
Best Practices for Securing Wireless Networks
Securing a wireless network requires attention to several critical factors. Here are the top 12 best practices to ensure your data and devices are safe from malicious actors:
- Secure the network through strong passwords and WPA2 encryption.
- Limit access to authorized devices only.
- Regularly update firmware and software.
- Monitor network activity and logs.
- Implement a guest network for visitors.
- Use a reputable and secure router.
- Use a VPN for remote access.
- Secure IoT devices.
- Use wireless intrusion detection and prevention systems.
- Regularly perform site surveys and coverage analysis.
- Implement a wireless security policy.
- Provide user education and training.
The Importance of Wireless Network Configuration
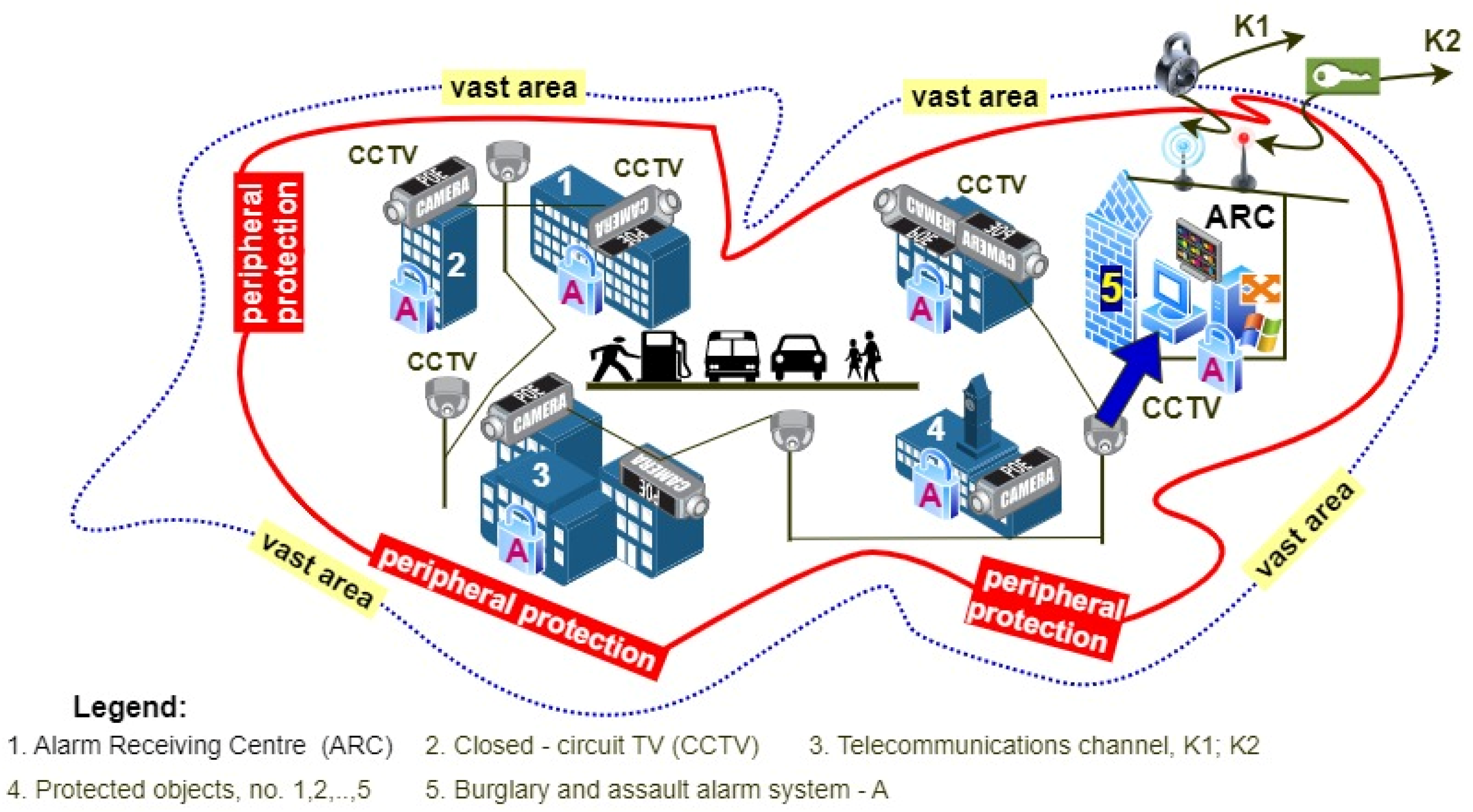
A wireless network configuration for security systems must consider the unique security requirements of these networks. An adversary could accumulate passwords or hashes from the configuration or local database by using a network analyzer or compromising a central management system that stores configuration files. It is essential to secure the configuration and ensure it is up-to-date and regularly updated.
WLAN Security and Performance Strategies
Understanding the practical aspects of setting up a wireless network is critical for security system administrators. Knowing the differences among WEP, WPA, WPA2, and WPA3 is essential for choosing the best encryption standard for your wireless network. Here's a brief comparison chart to help you make an informed decision.
| Encryption Standard | Security Level |
|---|---|
| WEP | Low |
| WPA | Medium |
| WPA2 | High |
| WPA3 | High |
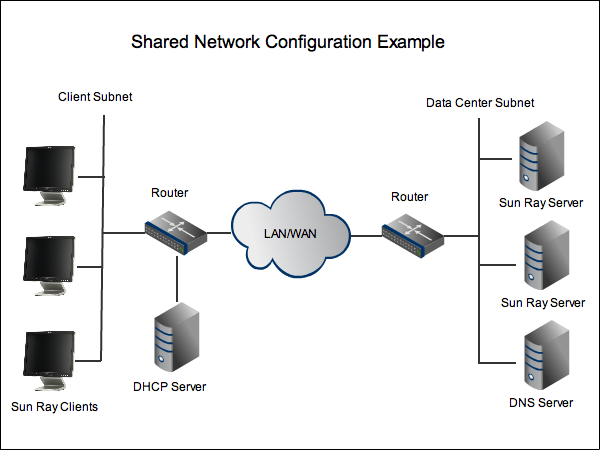
Secure Remote Access and Device Connection
Secure remote access and device connection are crucial for wireless network security. Here are the essential steps to follow:
- Configure secure remote access using a VPN.
- Ensure all devices connect to the wireless network securely.
- Regularly update device firmware and software.
Wireless Network Security Solutions
Companies like RUCKUS Networks offer advanced wireless network security solutions for enterprise environments. Their purpose-driven networks provide exceptional performance, security, and reliability. RUCKUS Networks is a leading provider of innovative and secure wireless network solutions for all kinds of enterprise environments.
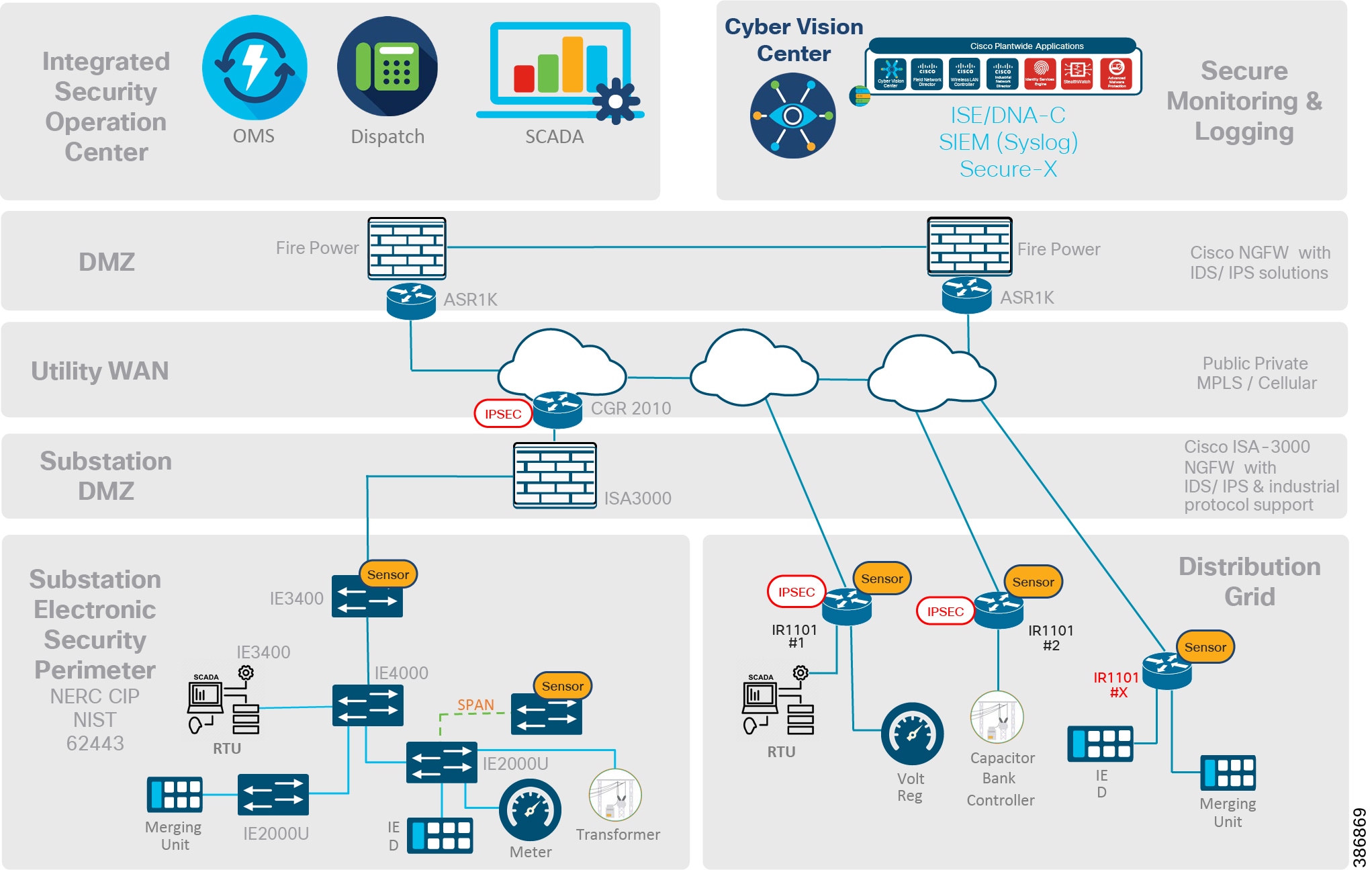
Best Practices for Industrial Wireless Deployments
Industrial wireless deployments require specialized solutions. The Wireless Distribution System (WDS) bridge is a critical component for high-performance networks. This system combines advanced 2.4 GHz wireless technology with industry-standard 5 GHz solutions to deliver world-class, reliable network performance.
SUMMARY
Securing a G wireless network configuration for security systems requires attention to several critical factors, including host-based security tools, best practices for securing wireless networks, wireless network configuration, WLAN security and performance strategies, secure remote access and device connection, and wireless network security solutions. By following these guidelines, administrators can ensure the safety and security of their wireless networks and the data stored on them.