Setup and Configuration of a G Wifi Network for Wireless Intrusion Prevention System
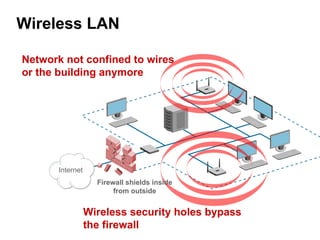
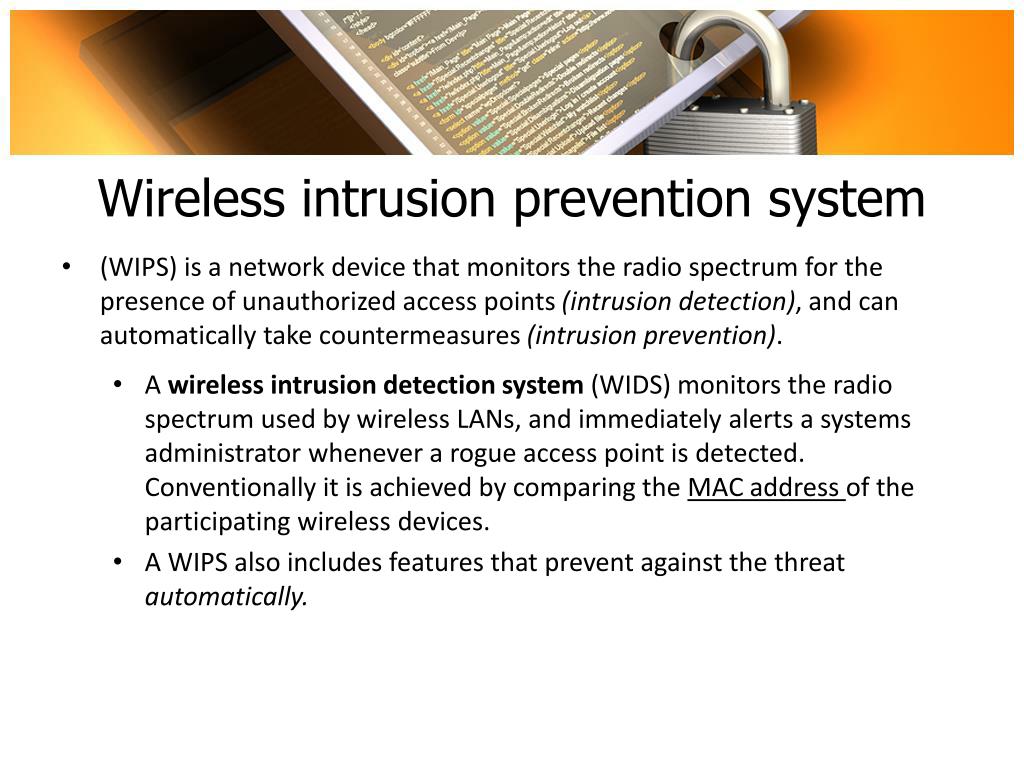
A wireless intrusion prevention system (WIPS) is a vital security tool that monitors a wireless local area network (WLAN) or Wi-Fi network's radio spectrum for rogue access points (APs) and other wireless threats. In this article, we will discuss how to set up and configure a G Wi-Fi network for wireless intrusion prevention system.
Hardware Requirements
To set up a WIPS, you will need the following hardware:
- Wireless access points (APs)
- Wireless routers or switches
- Wireless network interface controllers (WNICs)
- Network management station (NMS)
Software Requirements
The software requirements for setting up a WIPS include:
- Wireless intrusion prevention system (WIPS) software or application
- Wireless network management software
- Network operating system (NOS)
- Security protocols such as WEP, WPA, WPA2, or WPA3
Setup and Configuration of G Wi-Fi Network
To set up and configure a G Wi-Fi network for WIPS, follow these steps:
- Install and configure the wireless access points (APs) and wireless routers or switches.
- Configure the WNICs to connect to the wireless network.
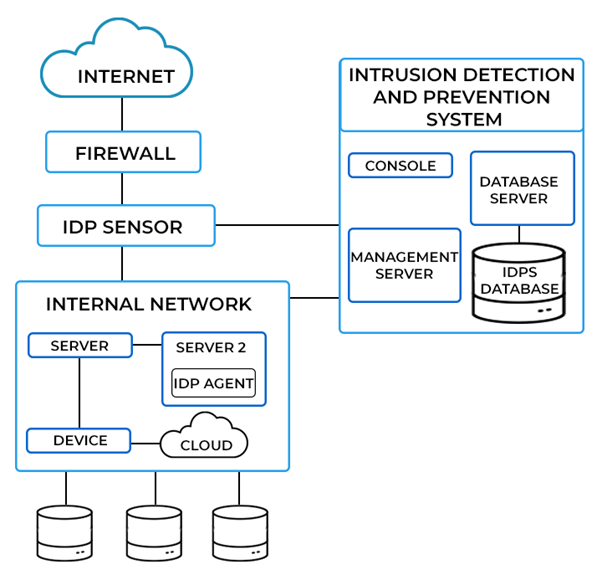
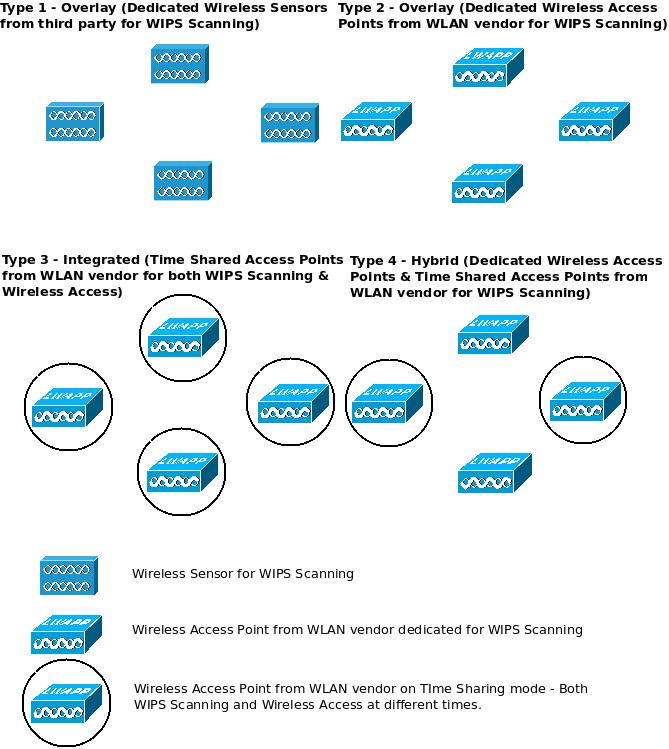
- Install and configure the WIPS software or application.
- Configure the wireless network management software to manage the WIPS and detect rogue APs.
- Configure the security protocols such as WEP, WPA, WPA2, or WPA3 to secure the wireless network.
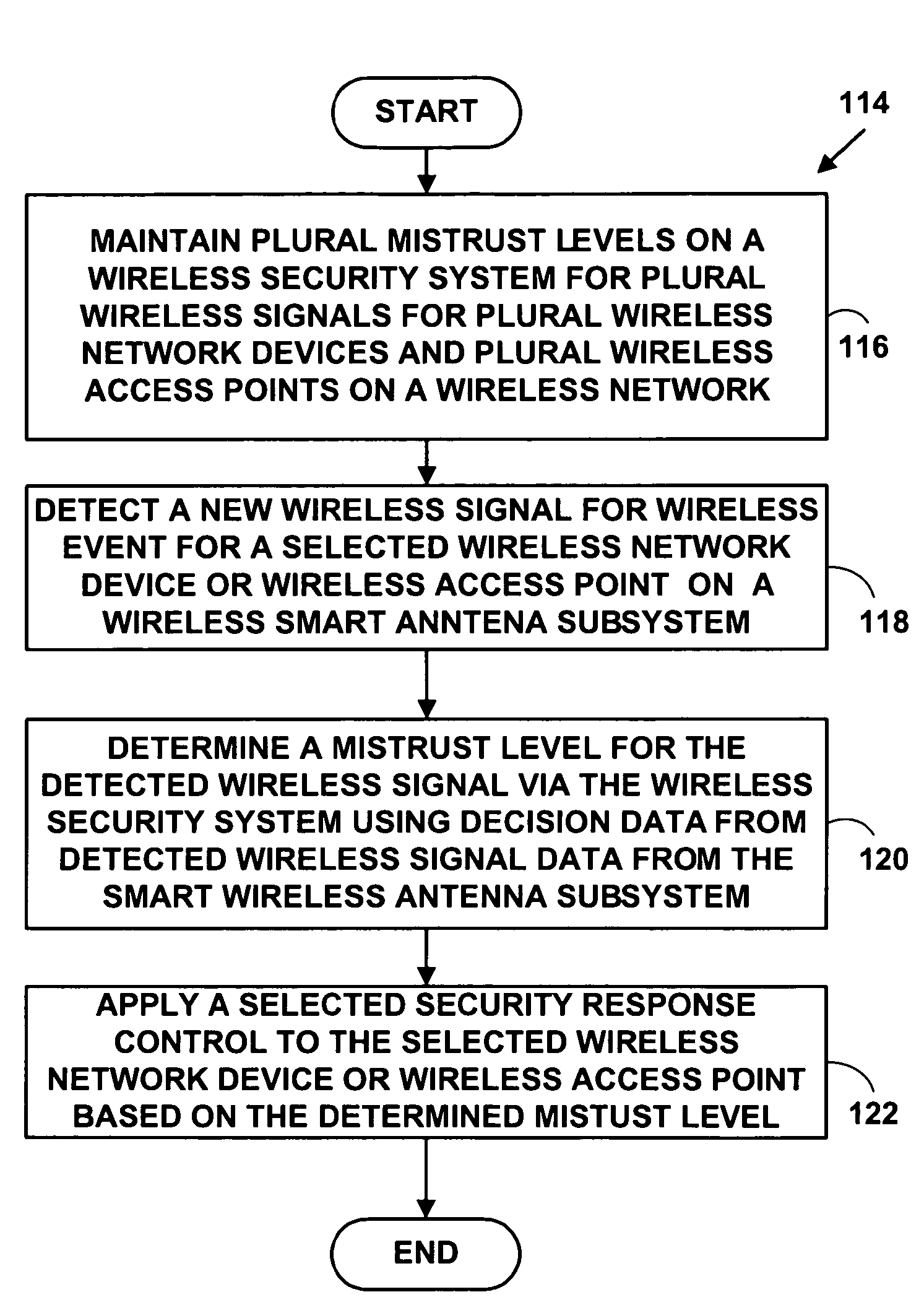
Configuration of WIPS
After setting up and configuring the G Wi-Fi network, configure the WIPS as follows:
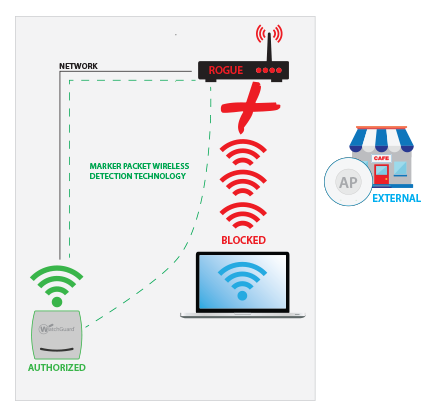
- Configure the WIPS to detect wireless threats such as rogue APs, suspicious wireless clients, and other potential threats.
- Configure the WIPS to monitor and block unauthorized access and security threats.
- Configure the WIPS to detect and prevent wireless attacks such as penetration attacks, denial-of-service (DoS) attacks, and man-in-the-middle (MitM) attacks.
- Configure the WIPS to provide alerts and notifications to network administrators in case of wireless threats or attacks.
- Configure the WIPS to provide detailed reporting and logs of wireless activity.
Best Practices for G Wi-Fi Network Setup and Configuration
Here are some best practices for G Wi-Fi network setup and configuration:
- Use strong security protocols such as WPA2 or WPA3.
- Use a secure password and encryption.
- Configure the WIPS to detect and prevent rogue APs and suspicious wireless clients.
- Configure the WIPS to monitor and block unauthorized access and security threats.
- Configure the WIPS to detect and prevent wireless attacks such as penetration attacks, DoS attacks, and MitM attacks.
- Configure the WIPS to provide alerts and notifications to network administrators in case of wireless threats or attacks.
- Configure the WIPS to provide detailed reporting and logs of wireless activity.
Conclusion
Setting up and configuring a G Wi-Fi network for wireless intrusion prevention system requires careful planning and execution. By following the steps outlined in this article, you can set up a robust and secure G Wi-Fi network that provides real-time protection against wireless threats and attacks.
Frequently Asked Questions
Here are some frequently asked questions about G Wi-Fi network setup and configuration for wireless intrusion prevention system:
- Q: What are the hardware requirements for setting up a G Wi-Fi network for WIPS?
- A: The hardware requirements include wireless access points (APs), wireless routers or switches, wireless network interface controllers (WNICs), and network management station (NMS).
- Q: What are the software requirements for setting up a G Wi-Fi network for WIPS?
- A: The software requirements include wireless intrusion prevention system (WIPS) software or application, wireless network management software, network operating system (NOS), and security protocols such as WEP, WPA, WPA2, or WPA3.
- Q: What is the configuration process for WIPS?
- A: The configuration process for WIPS involves configuring the WIPS software or application, wireless network management software, and security protocols to detect and prevent wireless threats and attacks.
- Q: What are some best practices for G Wi-Fi network setup and configuration?
- A: Some best practices include using strong security protocols such as WPA2 or WPA3, using a secure password and encryption, configuring the WIPS to detect and prevent rogue APs and suspicious wireless clients, and configuring the WIPS to provide detailed reporting and logs of wireless activity.